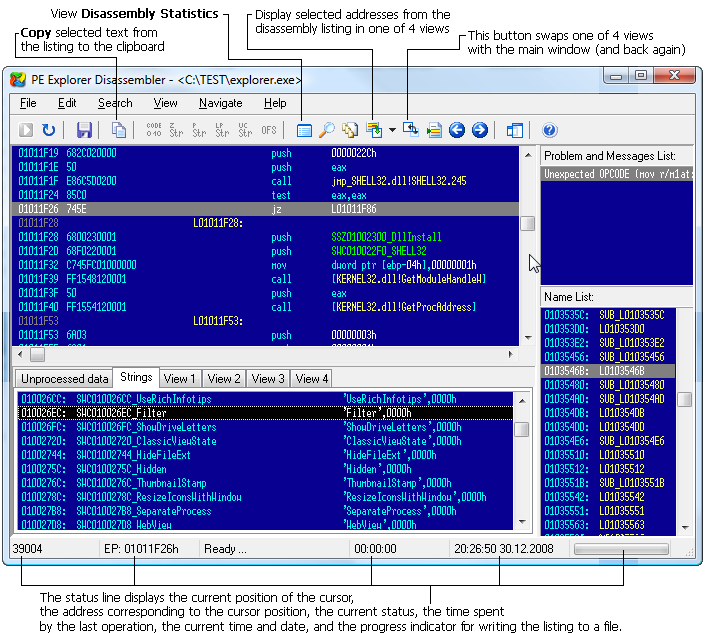
Disassembler For Exe Files
With a debugger you can step through the program assembly interactively. With a disassembler, you can view the program assembly in more detail.

With a decompiler, you can turn a program back into partial source code, assuming you know what it was written in (which you can find out with free tools such as - if the program is packed, you'll have to unpack it first OR if you can't find PEiD anywhere. DIE has a strong developer community on currently). Debuggers: •, free, a fine debugger, for which you can find numerous user-made plugins and scripts to make it all the more useful. •, free, a quite capable debugger by Microsoft. WinDbg is especially useful for looking at the Windows internals, since it knows more about the data structures than other debuggers. •, SICE to friends. Commercial and development stopped in 2006.
Download PE Explorer Binary header analyzer, resource hacking software and disassembler. Reverse engineer projects with missing. Download This release is. You can unzip it into the same directory as the non-gui decompiler; only the.exe. Quick usage: File New project; next to File to.
SoftICE is kind of a hardcore tool that runs beneath the operating system (and halts the whole system when invoked). SoftICE is still used by many professionals, although might be hard to obtain and might not work on some hardware (or software - namely, it will not work on Vista or NVIDIA gfx cards). Toshiba Gesture Controller Software. Disassemblers: • (commercial) - top of the line disassembler/debugger.
Used by most professionals, like malware analysts etc. City Bus Simulator Munich Crack. Costs quite a few bucks though (there exists, but it is quite quite limited) • (free) - a bit dated but gets the job done. I believe W32Dasm is abandonware these days, and there are numerous user-created hacks to add some very useful functionality.
You'll have to look around to find the best version. Decompilers: • Visual Basic:, commercial, produces somewhat identifiable bytecode. • Delphi:, free, produces good quality source code. • C:, commercial, a plugin for IDA Pro by the same company. Produces great results but costs a big buck, and won't be sold to just anyone (or so I hear). •.NET(C#):, free, decompiles.NET 1.0-4.5 assemblies to C#. Support for.dll,.exe,.zip,.vsix,.nupkg, and.winmd files.
Some related tools that might come handy in whatever it is you're doing are resource editors such as (free) and a good hex editor such as (commercial). Do Data.grf Ragnarok there. Additionally, if you are doing malware analysis (or use SICE), I wholeheartedly suggest running everything inside a virtual machine, namely.
In the case of SICE, it will protect your actual system from BSODs, and in the case of malware, it will protect your actual system from the target program. You can read about malware analysis with VMware. Personally, I roll with Olly, WinDbg & W32Dasm, and some smaller utility tools. Also, remember that disassembling or even debugging other people's software is usually against the EULA in the very least:). Psoul's excellent post answers to your question so I won't replicate his good work, but I feel it'd help to explain why this is at once a perfectly valid but also terribly silly question. After all, this is a place to learn, right? Modern computer programs are produced through a series of conversions, starting with the input of a human-readable body of text instructions (called 'source code') and ending with a computer-readable body of instructions (called alternatively 'binary' or 'machine code').
The way that a computer runs a set of machine code instructions is ultimately very simple. Each action a processor can take (e.g., read from memory, add two values) is represented by a numeric code. If I told you that the number 1 meant scream and the number 2 meant giggle, and then held up cards with either 1 or 2 on them expecting you to scream or giggle accordingly, I would be using what is essentially the same system a computer uses to operate. A binary file is just a set of those codes (usually call 'op codes') and the information ('arguments') that the op codes act on. Now, assembly language is a computer language where each command word in the language represents exactly one op-code on the processor. There is a direct 1:1 translation between an assembly language command and a processor op-code.
This is why coding assembly for an x386 processor is different than coding assembly for an ARM processor. Disassembly is simply this: a program reads through the binary (the machine code), replacing the op-codes with their equivalent assembly language commands, and outputs the result as a text file. It's important to understand this; if your computer can read the binary, then you can read the binary too, either manually with an op-code table in your hand (ick) or through a disassembler. Disassemblers have some new tricks and all, but it's important to understand that a disassembler is ultimately a search and replace mechanism. Which is why any EULA which forbids it is ultimately blowing hot air.